OpenClaw: What Security Teams Need to Know About “The Lobster”
OpenClaw: What Security Teams Need to Know About “The Lobster” January 2026 marked the...
In late 2025, technology news outlets reported the discovery of VoidLink, a sophisticated malware framework built specifically for cloud environments. According to The Hacker News, VoidLink was designed from the ground up for Linux-based infrastructure, targeting Kubernetes clusters and Docker containers. Unlike traditional malware adapted for cloud environments, this malware represents a shift in how attackers are focusing on containerized and multi-cloud workloads.
AI-Driven Development Accelerates Creation
News sources also highlighted that VoidLink’s development appears to have been assisted by AI tools. Infosecurity Magazine noted that analysis of the malware’s code revealed patterns consistent with AI-assisted generation, including structured sections and repetitive sequences that point to automated coding processes. Reports indicate that a single developer could produce an extremely large and modular codebase in a very short time. This demonstrates how artificial intelligence is enabling attackers to create complex cyber tools much faster than traditional methods.
How VoidLink Infects Cloud Systems
VoidLink is described by Bleeping Computer as a modular malware framework targeting Linux-based cloud environments. Rather than operating as a single static payload, it consists of structured components that include loaders, core implants, and multiple plugins designed to extend functionality after a system has been compromised.
According to the reporting, VoidLink enables attackers to deploy additional modules to an already infected system, allowing them to expand capabilities as needed. The framework is built using languages such as Zig, Go, and C, and demonstrates an organized development structure with extensive documentation and modular architecture.
This modular design allows attackers to maintain persistence and adapt functionality within compromised cloud systems, making the framework flexible and scalable for post-exploitation operations.
Why VoidLink Is a Critical Threat
VoidLink is not a single-purpose malware sample. It is a modular framework that allows attackers to dynamically extend functionality after gaining access to a cloud-hosted Linux system. Instead of deploying all capabilities at once, operators can selectively load plugins depending on their objectives.
Key Capabilities of VoidLink
Identifies the underlying cloud provider and determines whether it is running inside containerized environments such as Docker or Kubernetes.
Adjusts behavior based on detected security monitoring tools to reduce the likelihood of triggering alerts.
Uses eBPF-based methods on modern Linux kernels to conceal activity, and falls back to techniques such as LD_PRELOAD hijacking or loadable kernel modules on older systems.
Supports dozens of extensions that can be deployed post-compromise, enabling tailored operations.
Extracts authentication material from compromised systems to expand attacker access.
Assists attackers in pivoting across servers within the same cloud environment.
Maintains access even after reboots or service restarts.
Includes capabilities designed to remove traces of activity or self-delete if tampering is detected.
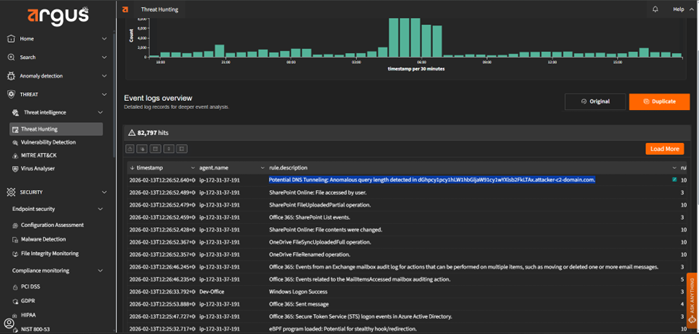
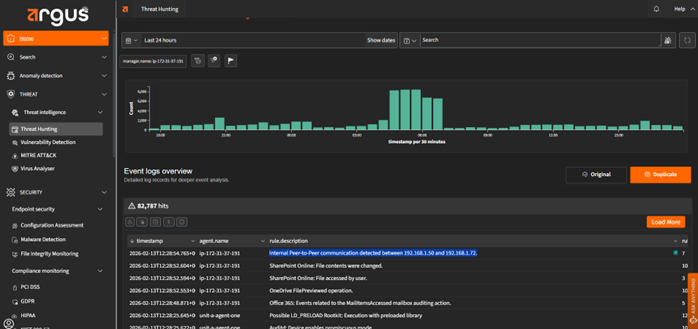
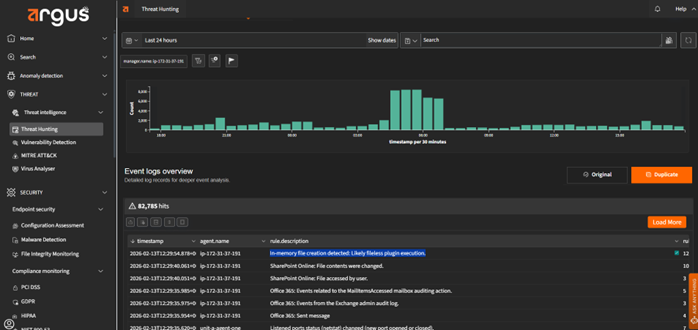
Next, we demonstrate how Argus, our AI-first Cyber Threat and Exposure Detection, Analysis, and Remediation platform, detects a VoidLink intrusion within a cloud environment.
How Argus Detects a VoidLink Cloud Intrusion
VoidLink malware often infects Linux or Unix systems by preloading malicious shared libraries, typically using mechanisms like LD_PRELOAD. This allows the malware to execute its code before the legitimate program runs, intercept system calls, steal data, and spread to other systems.
Argus continuously monitors process initiation and evaluates environment variables and library-loading behavior. When it detects unauthorized or abnormal use of preloaded shared libraries, it raises an alert. Because legitimate applications rarely rely on suspicious or undocumented preload mechanisms, this behavior serves as a strong indicator of compromise. By identifying anomalous library injection at execution time, Argus can detect VoidLink’s stealth techniques early in the attack chain.
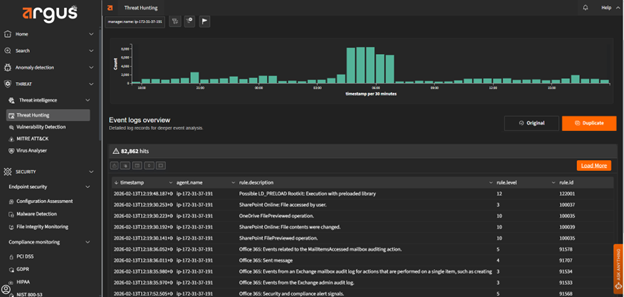
Malware that seeks deep system control may attempt to load a kernel module using utilities such as insmod or modprobe. Kernel modules operate at the core of the operating system, giving them privileged access to system memory, processes, and network activity. If an unauthorized or malicious module is inserted, it can hide files, intercept system calls, manipulate logs, or establish persistent backdoor access. Because kernel modules function at such a low level, their misuse often indicates an advanced compromise attempt.
Argus continuously monitors kernel-level events, including module insertion activity. When a new kernel module is loaded, Argus validates its legitimacy and flags unusual, unsigned, or unauthorized insertions in real time. By detecting suspicious module loading behavior early, Argus helps prevent attackers from gaining persistent, kernel-level control and limits the risk of stealth rootkit-style attacks.
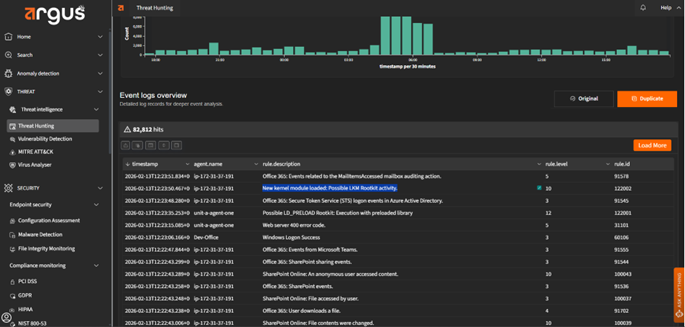
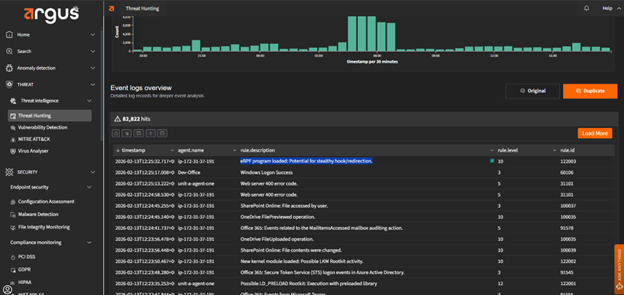
Advanced malware may attempt to load eBPF (extended Berkeley Packet Filter) programs into the Linux kernel to intercept, monitor, or manipulate system calls. Because eBPF operates within the kernel space, it allows highly granular visibility and control over system behavior. When misused, eBPF can be leveraged to hide malicious processes, conceal network connections, capture sensitive data, or modify runtime behavior without leaving obvious user-space artifacts. Unauthorized or unusual eBPF loading activity is therefore a strong indicator of sophisticated intrusion attempts.
Argus continuously monitors the loading of eBPF programs and analyzes their behavior in real time. When it detects unexpected or unauthorized eBPF activity, especially programs attempting to hook or alter system calls, it generates an alert for investigation. By identifying abnormal kernel-level instrumentation early, Argus helps prevent stealth persistence, covert monitoring, and data exfiltration attempts associated with advanced threats.
VoidLink relies on covert network channels to maintain command-and-control communication and coordinate activity across compromised systems. Its modular architecture allows operators to retrieve plugins, issue commands, and potentially move laterally within cloud environments. To avoid detection, these communications may blend into legitimate traffic patterns, including the use of DNS-based signaling or internal peer-to-peer connections over non-standard ports.
Argus continuously analyzes network behavior to detect indicators consistent with VoidLink’s communication patterns. It identifies anomalous DNS activity that may signal hidden command exchanges or data exfiltration attempts, and it flags unusual internal IP-to-IP communication that deviates from expected service behavior. By detecting covert C2 signaling and unauthorized lateral communication early, Argus helps contain VoidLink before it can expand control or compromise additional cloud workloads.
VoidLink can execute components directly in memory rather than writing them to disk. This fileless execution approach reduces forensic artifacts and helps the framework evade traditional antivirus solutions that rely on file-based signatures or disk scanning. By running plugins or loaders entirely in RAM, VoidLink minimizes its visible footprint while maintaining operational control within the compromised system.
Argus monitors system-level execution events associated with in-memory activity, including the memfd_create system call tied to the audit key mem-exec. When a process attempts to execute a program directly from memory, Argus records and analyzes the event in real time. Because legitimate applications rarely rely on anonymous in-memory execution mechanisms for persistent operations, such activity serves as a high-confidence indicator of stealth behavior. By tracking these memory-resident execution patterns, Argus can surface fileless components of VoidLink that might otherwise evade traditional detection methods.
VoidLink reflects how modern threats are evolving alongside cloud infrastructure. It is modular, adaptive, and designed to blend into complex Linux environments rather than announce its presence. That shift alone changes how organizations must think about detection. Traditional tools that rely heavily on static indicators struggle against frameworks that execute in memory, adjust to kernel versions, and communicate covertly.
The real takeaway is not just that VoidLink is sophisticated, but that cloud-native threats are becoming operationally aware and strategically stealthy. Defending against them requires visibility across processes, kernel activity, and network behavior, not just files on disk.
By continuously analyzing these behavioral layers, Argus helps security teams detect the techniques that power threats like VoidLink, even as the framework evolves.
Interested in a live demo? Fill out the contact form, and our team will respond within 24 hours.
OpenClaw: What Security Teams Need to Know About “The Lobster” January 2026 marked the...
VoidLink Malware Under Watch: Argus’ Approach to Cloud-Native Malware In late 2025, technology news...
Verticalized Threats: How Modern Malware Targets Specific Industries Cyber threats today are not defined...
Stay informed with bi-monthly insights and news.
Copyright © 2025 Argus. All rights reserved.
Fill out the form below!