The Hidden RAT: Detecting PureHVNC with Argus by Genix Cyber
The Hidden RAT: Detecting PureHVNC with Argus by Genix Cyber What is PureHVNC The...

What is PureHVNC
The Pure malware family highlights how cybercrime continues to evolve into a structured and scalable ecosystem. Developed by an actor known as PureCoder, this suite brings together multiple malicious tools that support different stages of an attack lifecycle, from initial compromise to data exfiltration and persistence.
At its core is PureHVNC, a Remote Access Trojan (RAT) designed to give attackers covert control over compromised systems. It uses Hidden Virtual Network Computing (HVNC) to operate within an invisible desktop environment, allowing threat actors to execute actions, monitor activity, and interact with applications without the user’s knowledge. This approach enables highly stealthy operations, including session hijacking and fraudulent transactions, while avoiding traditional detection mechanisms.
Threat actors actively promote and distribute the Pure suite through underground forums, Telegram channels, and dedicated websites. This accessibility enables even low-skilled operators to launch advanced attacks with minimal effort. By packaging these capabilities into an integrated offering, the Pure malware family lowers the barrier to entry and amplifies the scale and impact of modern cyber threats.
PureHVNC typically relies on user-driven infection vectors, where the attacker tricks the victim into executing the malware. Threat actors focus on delivery methods that appear legitimate and require minimal technical exploitation.
Phishing and Malicious Attachments
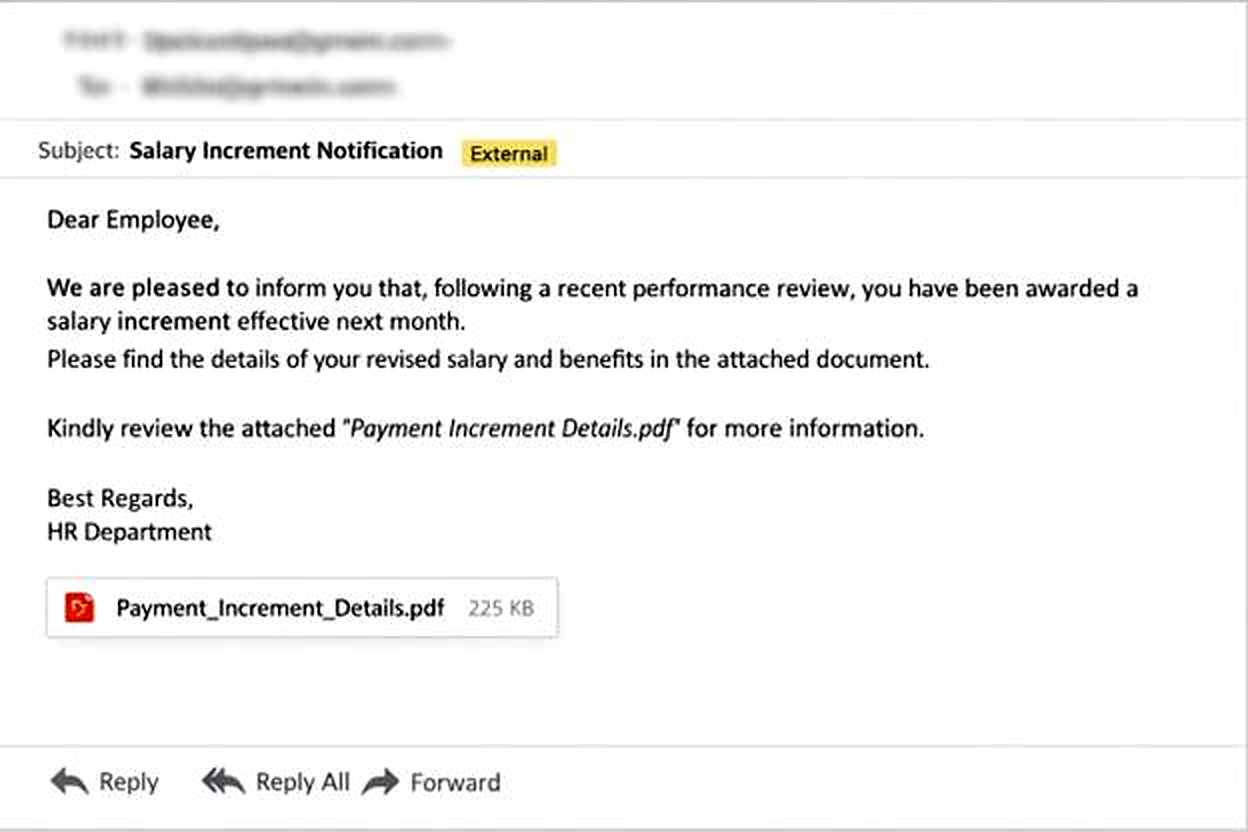
Attackers commonly distribute PureHVNC through phishing emails that contain malicious attachments or links. These attachments often masquerade as:
The files may appear as PDFs, Word documents, or compressed archives. In many cases, the actual payload hides within an executable disguised with a misleading icon or double extension.
Bundled Malware and Loaders
Threat actors frequently package PureHVNC with loaders or crypters such as PureCrypter. These tools obfuscate the payload and help it evade antivirus detection.
The user typically downloads and executes what appears to be legitimate software, such as:
Once executed, the loader silently deploys PureHVNC in the background.
Malicious Downloads and Drive-By Delivery
In some campaigns, attackers host infected files on file-sharing platforms or compromised websites. Users download these files directly, believing them to be legitimate resources.
Attackers may also use fake software updates or browser prompts to convince users to download and run the payload.
Social Engineering as the Primary Enabler
PureHVNC does not rely heavily on zero-day exploits. Instead, it depends on social engineering to bypass security controls. The attacker’s success depends on convincing the user to execute the initial file.
This approach makes the malware highly scalable, as it can target a broad range of users without requiring complex exploitation techniques.
Once PureHVNC executes on a Windows system, it follows a structured sequence to establish control, deploy its components, and remain hidden throughout the process.
Initial Execution and User Distraction
The malware begins by downloading and opening a decoy PDF document. This tactic diverts the user’s attention and creates the appearance of legitimate activity. While the document loads, the malware silently initiates its setup routine in the background.
In some cases, it introduces a short delay using commands such as timeout.exe /t 5. This ensures the decoy file opens first, reinforcing the illusion of benign behavior before any malicious activity becomes noticeable.
Retrieval of Additional Payloads
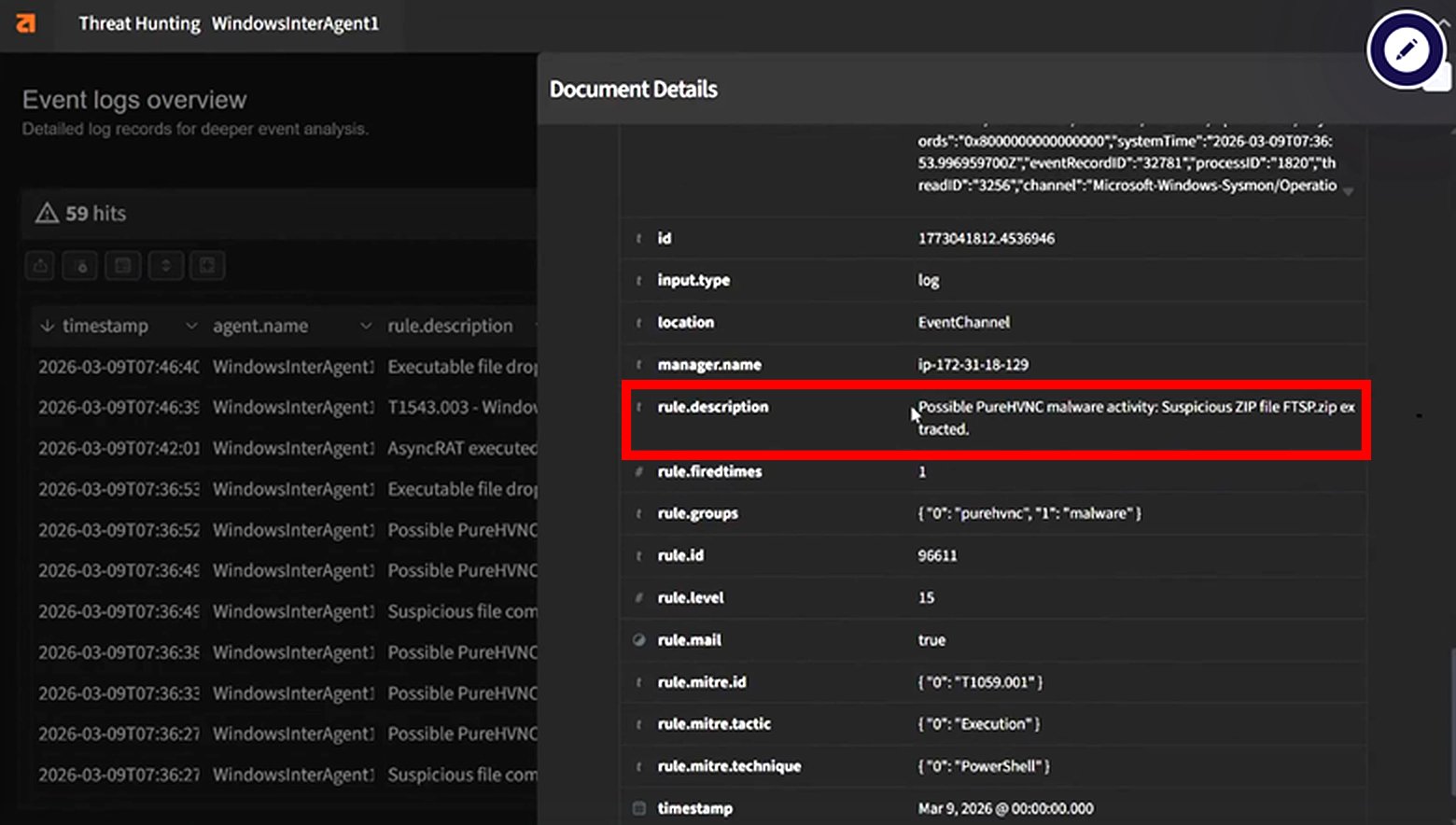
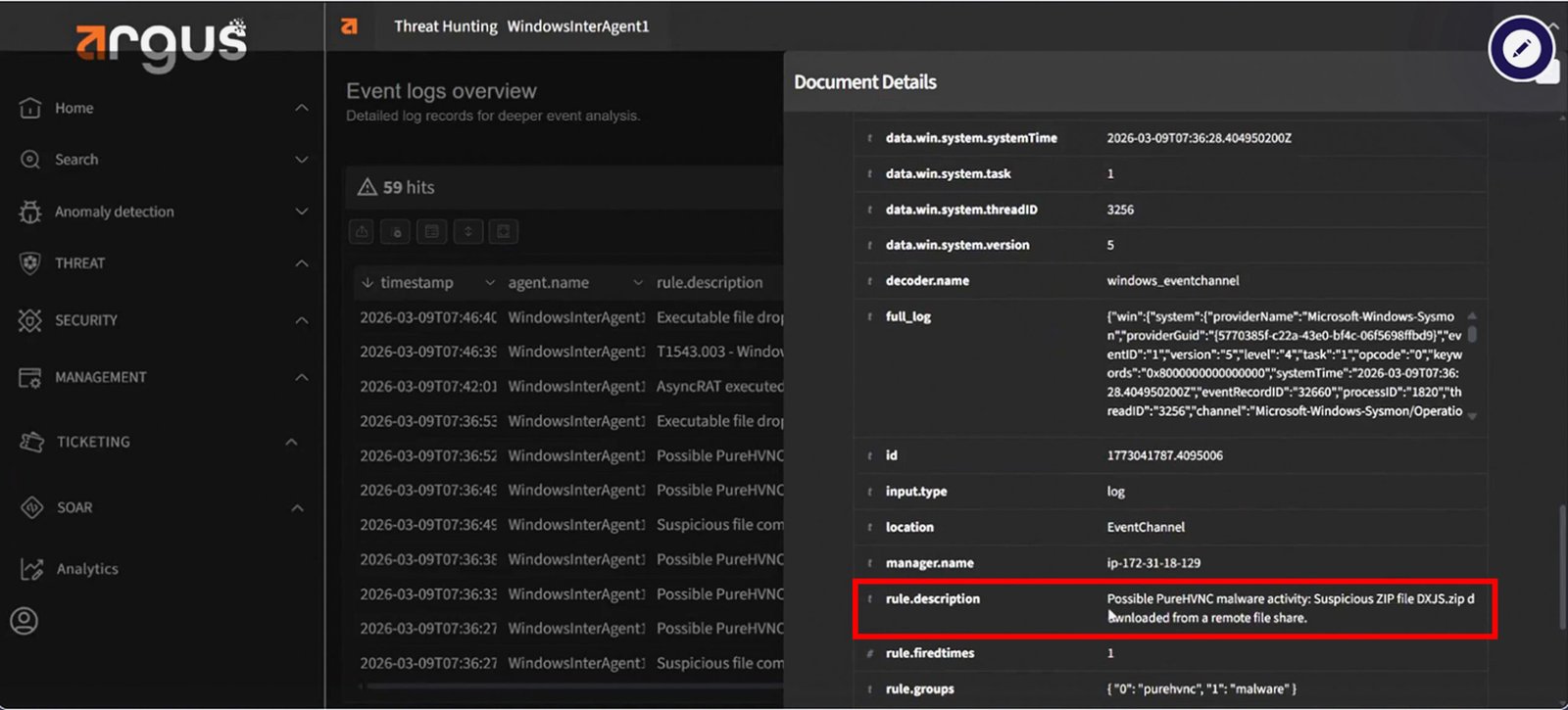
After execution, the malware proceeds to download additional components from remote infrastructure. It typically retrieves compressed archives such as:
It uses built-in tools like PowerShell, often leveraging commands such as Invoke-WebRequest, to pull these files from external file-sharing or staging servers. These archives contain the modules required to expand functionality and establish deeper control over the infected system.
Stealthy File Extraction and Storage
The malware extracts the downloaded archives into directories within the user’s system, commonly under the Downloads path. Examples include:
To reduce visibility, it modifies file attributes using commands like attrib +h, marking these folders as hidden. This step ensures that standard file browsing does not reveal the presence of these components unless hidden files are explicitly enabled.
Execution of Embedded Scripts
The extracted content includes multiple Python scripts, each designed to perform specific operational tasks. Common examples include:
The malware executes these scripts through a bundled or system-level Python interpreter. Each script contributes to the attack lifecycle, enabling persistence, collecting system and user data, handling file transfers, and preparing the environment for sustained remote access.
Command-and-Control Communication
Once the environment is fully prepared, PureHVNC establishes communication with an external command-and-control (C2) server. This connection enables the attacker to issue instructions and control the infected system in real time.
From this point, the attacker can:
Because PureHVNC operates through a hidden virtual desktop environment, all attacker activity remains invisible to the user. This level of stealth allows threat actors to maintain persistence and conduct operations without raising suspicion.
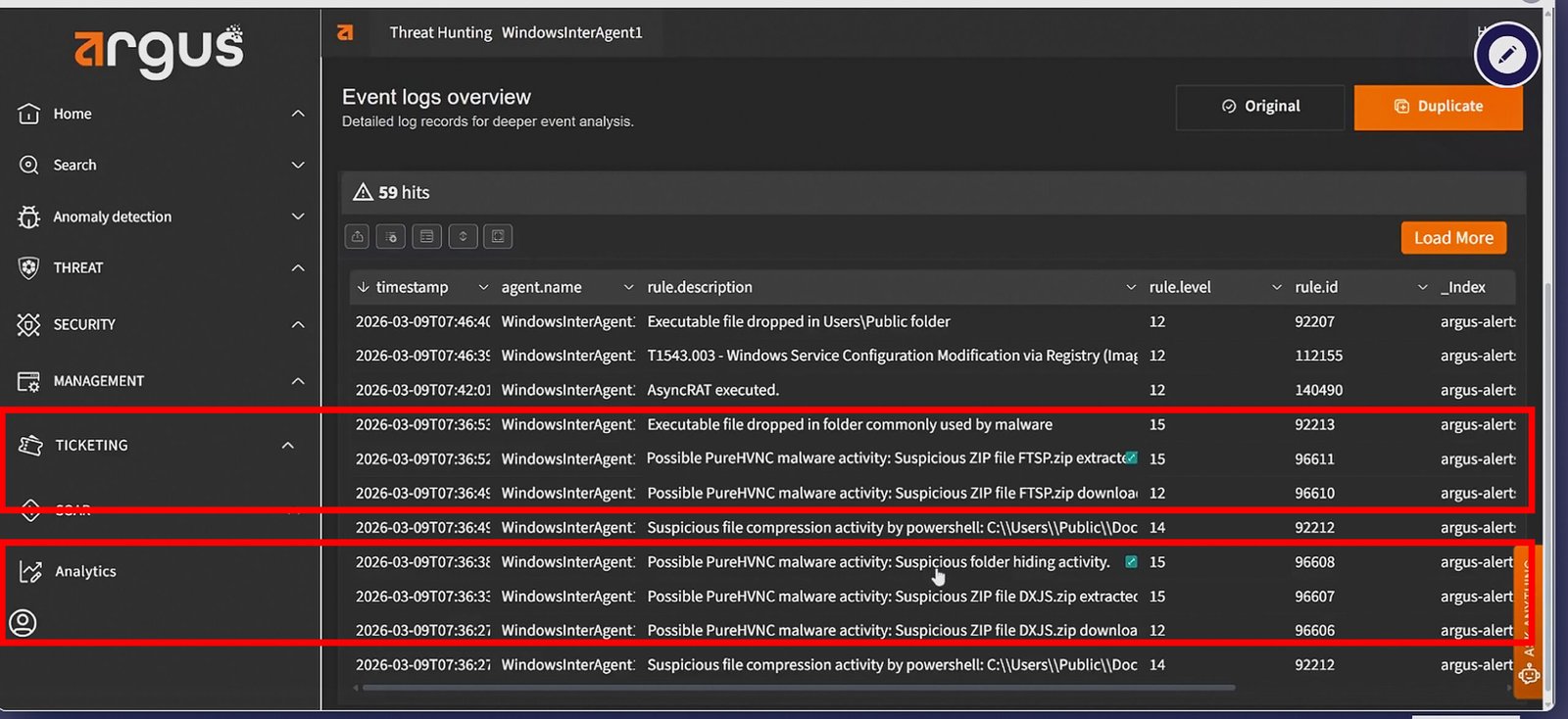
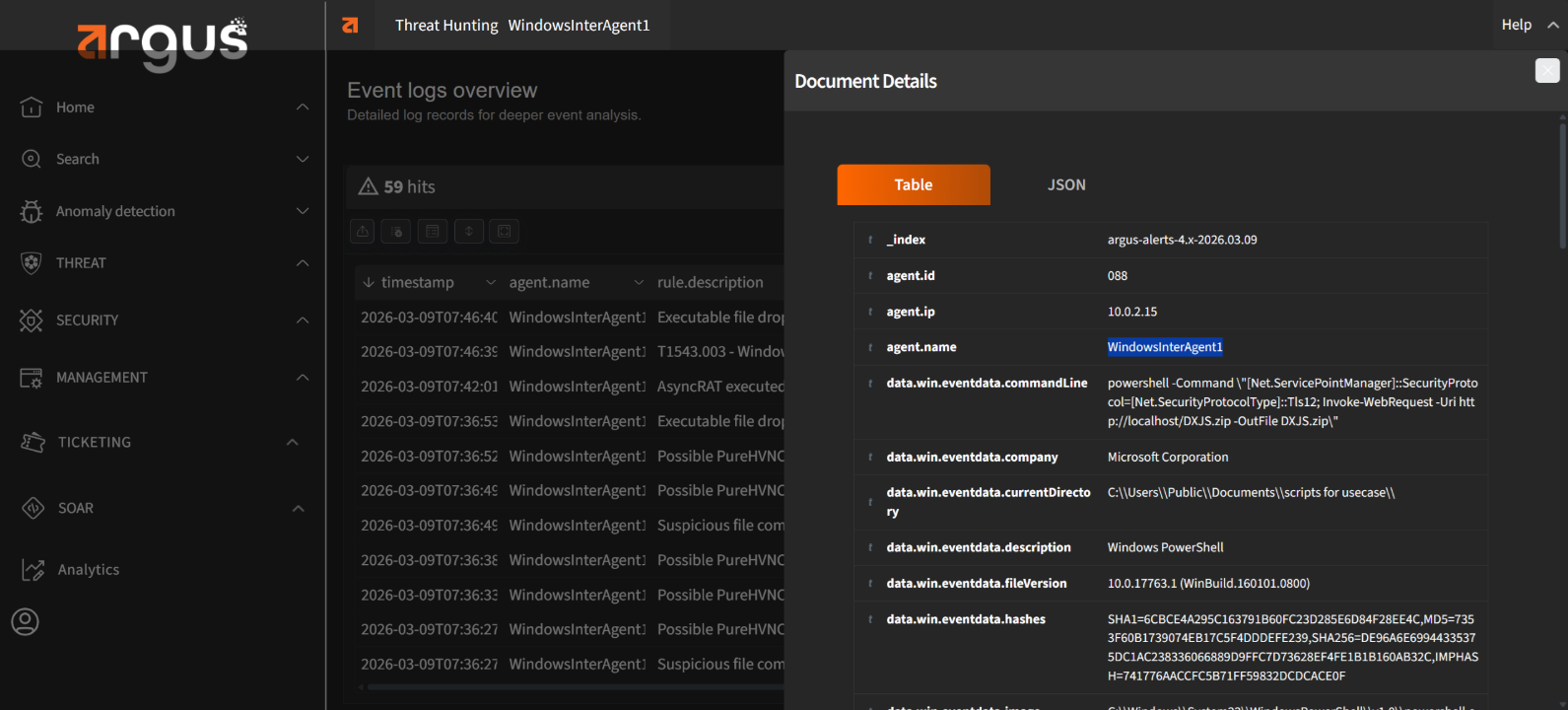
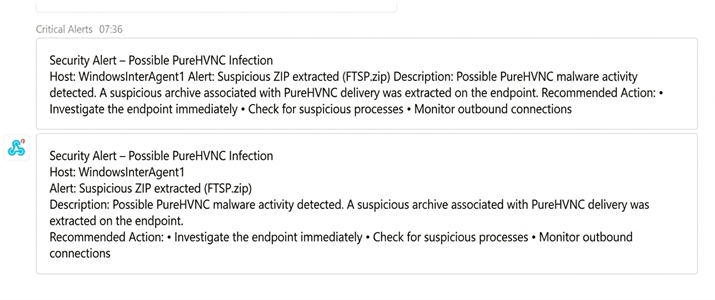
Now, we will demonstrate how Argus stops Pure HVNC
PureHVNC reflects a broader shift in how threat actors operate today. They no longer rely on isolated tools or complex exploits. Instead, they leverage packaged, ready-to-use ecosystems that prioritize stealth, scalability, and ease of deployment.
This shift places pressure on organizations to rethink how they detect and respond to threats. Traditional approaches that depend on delayed analysis or signature-based detection struggle to keep pace with fast-moving, evasive malware.
This is where instant detection and real-time response become essential. Identifying suspicious behavior at the point of execution and acting immediately can prevent an incident from turning into a breach.
Argus enables this level of responsiveness by continuously analyzing activity at the endpoint, surfacing high-confidence alerts, and pushing them directly into channels where teams already operate. This allows security teams to move quickly, coordinate effectively, and contain threats before they gain a foothold.
In an environment where attackers optimize for speed and invisibility, defense must do the same. The ability to detect early and respond instantly is what ultimately shifts the advantage back to the defender.
The Hidden RAT: Detecting PureHVNC with Argus by Genix Cyber What is PureHVNC The...
LockBit 5.0: Anatomy of a Modern Ransomware Operation Ransomware remains one of the most...
OpenClaw: What Security Teams Need to Know About “The Lobster” January 2026 marked the...
Stay informed with bi-monthly insights and news.
Copyright © 2025 Argus. All rights reserved.
Fill out the form below!