OpenClaw: What Security Teams Need to Know About “The Lobster”
OpenClaw: What Security Teams Need to Know About “The Lobster” January 2026 marked the...

Cybercriminals constantly evolve their tools to bypass defenses, and GoBruteforcer represents one of the most sophisticated brute-force malware threats today. Unlike malware that exploits software vulnerabilities, GoBruteforcer focuses on credential-based attacks, automatically attempting to guess passwords to gain access to servers. Security researchers classify it as a botnet because compromised systems become part of a network that expands the malware’s reach.
GoBruteforcer is written in the Go programming language, which allows it to run on multiple architectures such as x86, AMD64, and ARM. This cross-platform capability enables attackers to target a wide range of Linux servers, including cloud-based and containerized systems. Its design allows the malware to operate efficiently, avoid detection, and propagate across networks without direct human intervention.
GoBruteforcer primarily scans internet-facing services that use default or weak credentials. Researchers have observed it targeting FTP servers, MySQL and PostgreSQL databases, and phpMyAdmin interfaces. It also identifies cloud instances and containerized environments, taking advantage of poorly managed credentials and exposed services.
Attackers focus on systems with high-value data, including cryptocurrency wallets, sensitive databases, and servers capable of acting as relays for future attacks. The malware can operate silently on compromised systems, hiding its activities while continuing to scan and attack other targets. Each infected server contributes to the botnet, multiplying the threat’s reach and scale.
GoBruteforcer follows a systematic attack flow designed for automation and stealth.
Argus by Genix Cyber is built as a unified security ecosystem, not a collection of stitched-together tools. It continuously monitors authentication behavior, network activity, and system events to detect anomalies in real time. Instead of reacting after compromise, Argus identifies attack patterns early and stops threats before they escalate.
Let’s examine how Argus detects GoBruteForcer activity at the initial access stage.
GoBruteForcer begins by scanning internet-facing services such as SSH, FTP, and MySQL. It then launches automated login attempts using commonly targeted usernames, including crypto-themed accounts like cryptouser or appcrypto, paired with password lists.
Argus continuously monitors authentication activity across these services to detect abnormal behavior, such as:
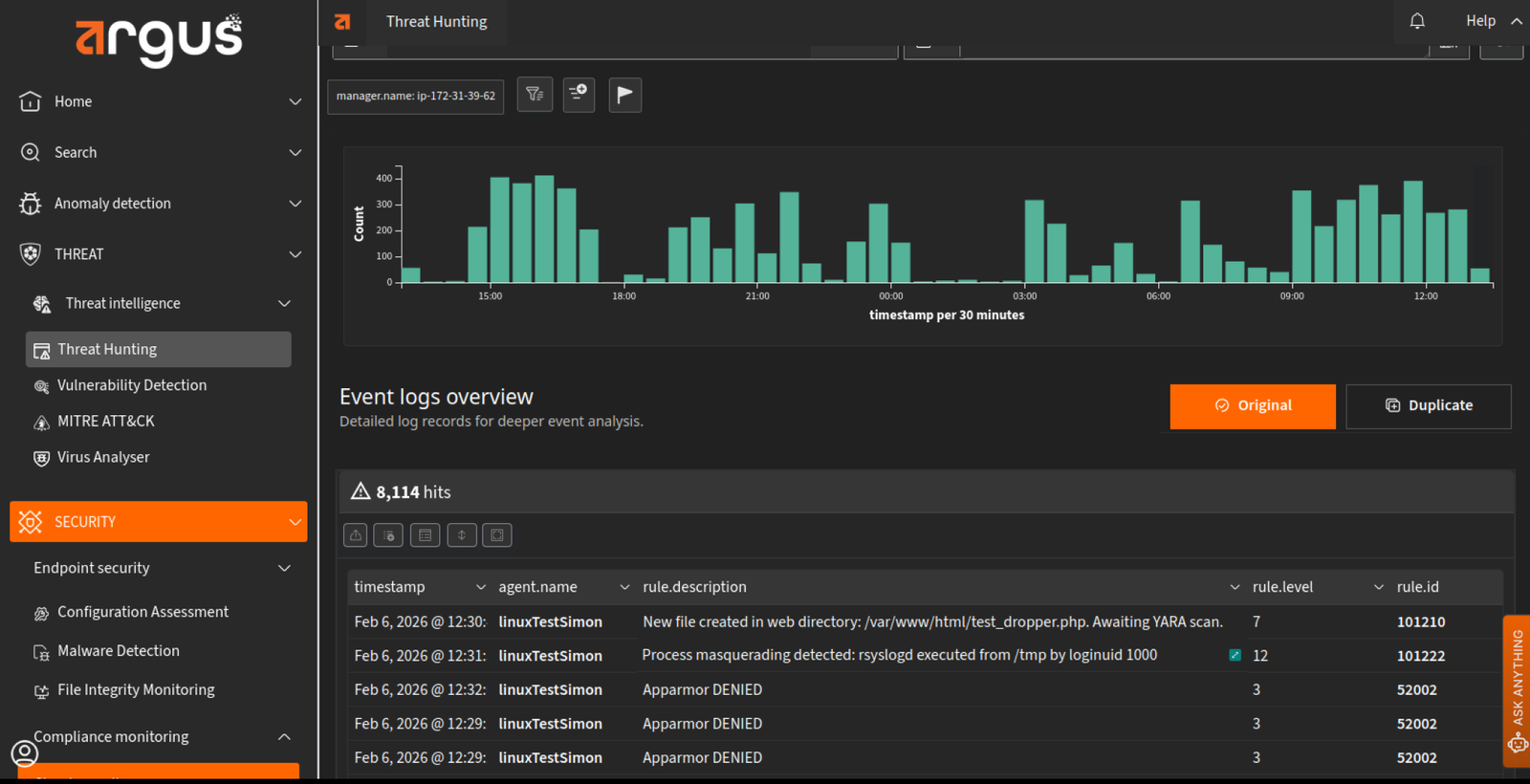
When these patterns are detected, Argus immediately generates alerts and visualizes the activity on the Threat Hunting Dashboard. Security teams can quickly identify potential brute-force campaigns, contain the source, and prevent servers from being compromised or incorporated into botnets.
By tracking attempts to access SSH and FTP services through brute-force attacks, Argus ensures that even stealthy credential-stuffing campaigns are identified and blocked in real time. Alerts from simulated attack tests appear instantly on the dashboard, enabling rapid response before any unauthorized access occurs.
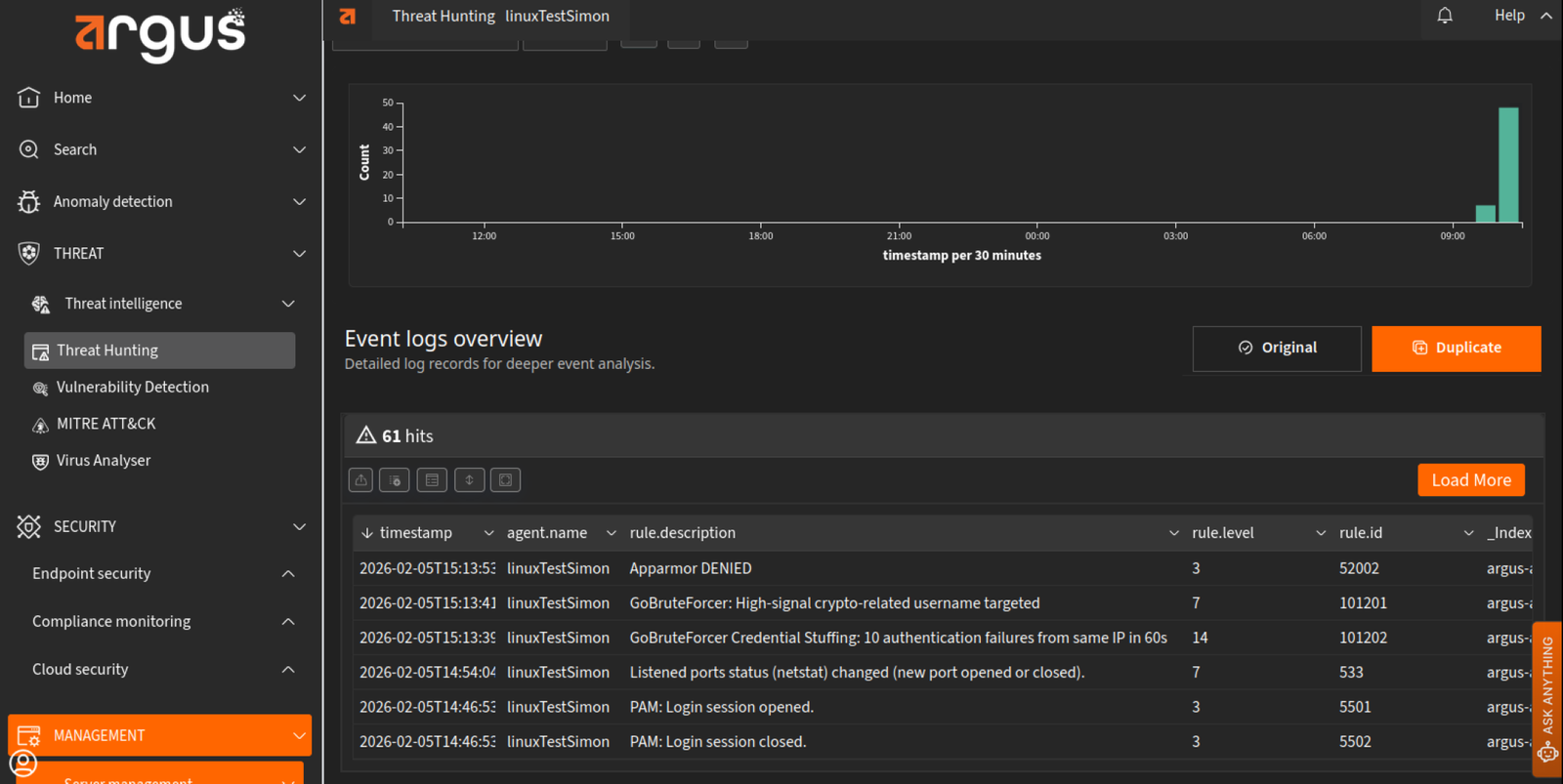
GoBruteForcer SSH and SSH bruteforce detection alert shown within the Threat Hunting Dashboard on Argus after SSH attack test simulation
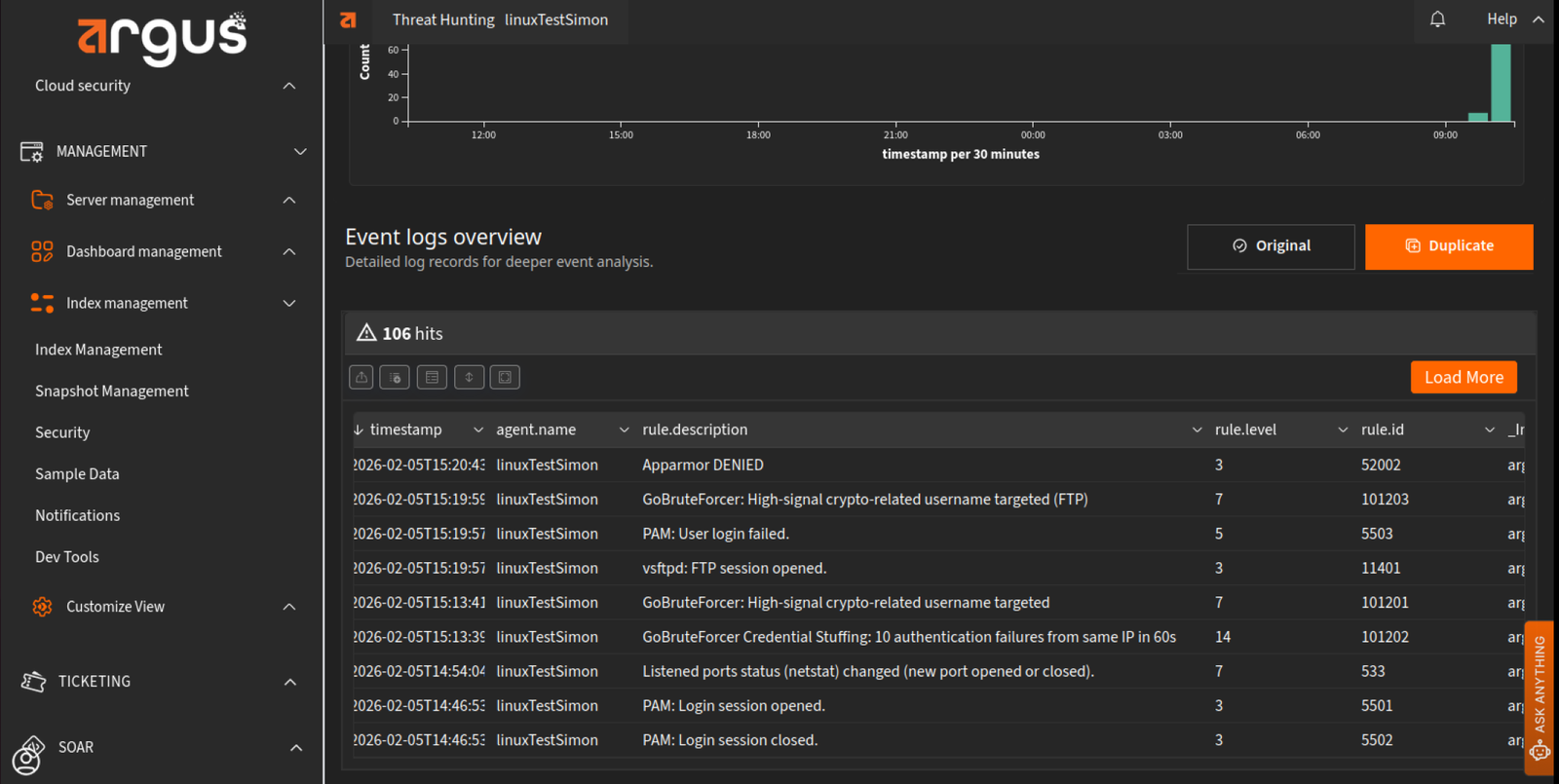
GoBruteForcer FTP alert shown within the Threat Hunting Dashboard on Argus after FTP attack test simulation
After attackers compromise credentials on targeted services, they often upload a PHP dropper webshell to fingerprint the system’s operating system and architecture and deliver the appropriate malware.
Argus provides real-time file integrity monitoring to detect such activity within commonly targeted directories. For example, when a PHP webshell is uploaded to /var/www/html, Argus immediately triggers alerts on the Threat Hunting Dashboard.
Two distinct alerts are generated:
This capability allows security teams to quickly identify post-compromise activity, investigate the affected systems, and respond before malware can execute further operations, effectively stopping lateral movement and persistence attempts.
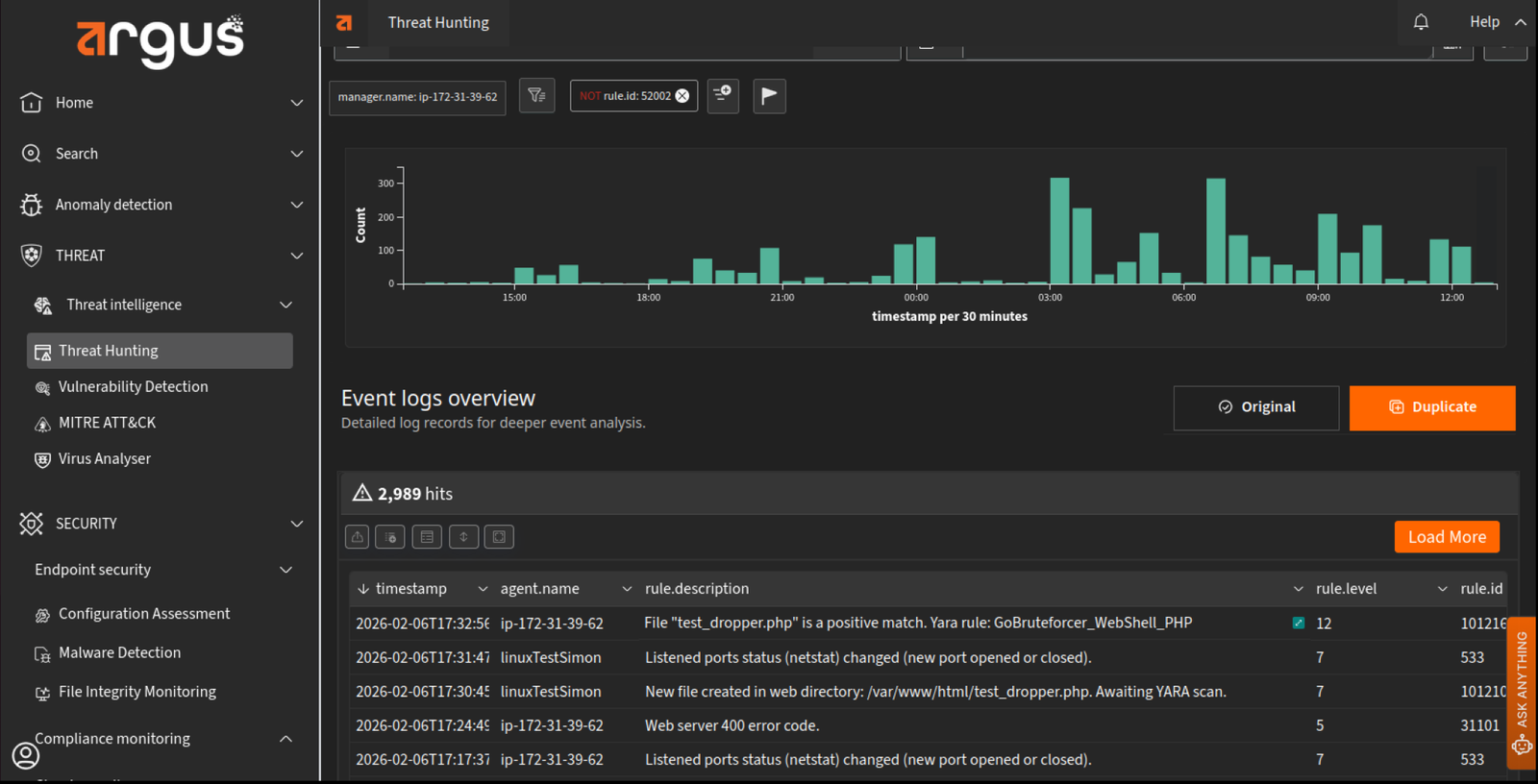
Two alerts trigger on the Threat Hunting dashboard. One indicates the discovery of a new file created into the monitored directory and the other indicates a positive match to the GoBruteForcer_Webshell_PHP.
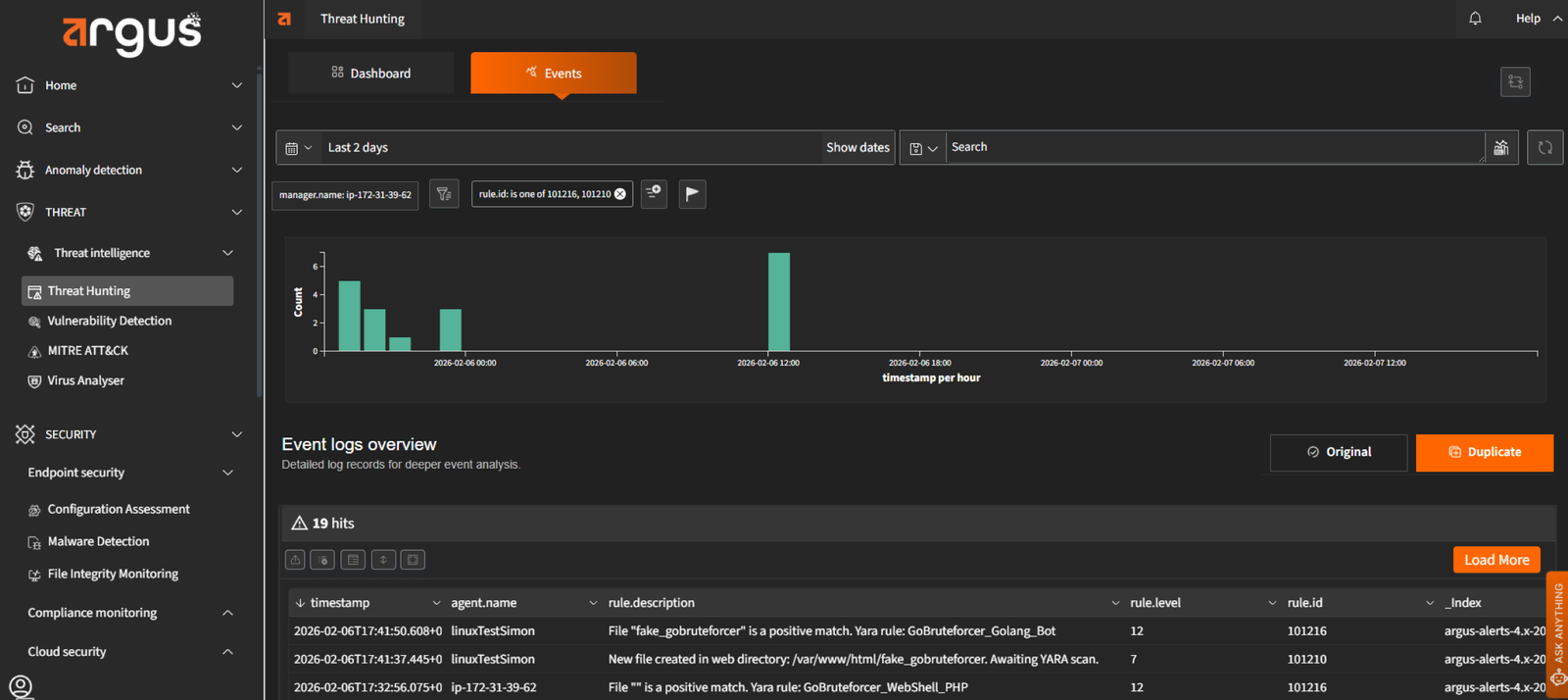
The GoBruteForcer core payload is delivered as a statically compiled Golang binary, supporting multiple architectures including x86, x64, and ARM. Once executed, it establishes an IRC-based Command and Control (C2) connection and includes modules for activities such as scanning for TRON blockchain wallets and attempting brute-force attacks on other servers.
Argus continuously monitors system activity and detects the execution of such Golang binaries in real time. Alerts are displayed on the Threat Hunting Events Dashboard, providing security teams with immediate visibility into malicious payload activity and enabling rapid investigation and containment before the malware can perform further operations or propagate laterally..
Once the GoBruteForcer payload is deployed, it attempts to maintain persistence by creating scheduled tasks via crontab and begins scanning the local network to propagate to other systems. To evade detection, it often renames itself to mimic legitimate system services, such as rsyslogd or kworker.
Argus continuously monitors key directories and system processes to detect anomalies, including:
By correlating these indicators in real time, Argus alerts security teams to lateral movement and persistence activity, enabling rapid containment and preventing further compromise across the network.
GoBruteForcer attacks progress through multiple stages, including credential stuffing, webshell deployment, payload execution, and lateral movement to compromise systems. Argus delivers comprehensive, real-time monitoring and detection across each stage of the attack, ensuring that malicious activity is identified immediately.
By analyzing authentication anomalies, changes in file integrity, suspicious binary execution, and unusual process behavior, Argus provides security teams with complete visibility into ongoing attacks. This proactive monitoring stops GoBruteForcer campaigns before they escalate, preventing servers from being recruited into botnets or spreading malware further.
With Argus, organizations benefit from a unified defense platform that continuously monitors, detects, and responds to threats. This allows teams to maintain security while keeping systems operational, even against sophisticated and stealthy attacks like GoBruteForcer.
OpenClaw: What Security Teams Need to Know About “The Lobster” January 2026 marked the...
VoidLink Malware Under Watch: Argus’ Approach to Cloud-Native Malware In late 2025, technology news...
Verticalized Threats: How Modern Malware Targets Specific Industries Cyber threats today are not defined...
Stay informed with bi-monthly insights and news.
Copyright © 2025 Argus. All rights reserved.
Fill out the form below!